When it comes to printer security, sometimes it can get a low priority. Printers used to, well, just print. Now, printers can scan a document to cloud storage, print by voice commands, or let the manufacturer know when you’re low on ink.
All these conveniences come with a hidden price. Security is sacrificed for ease of use. A printer contacting a manufacturer for ink is great. However, the printer is exposed to the internet and all its risks.
If you’ve ever wondered what you can do to make a multi function printer more secure, this article will help. If we’re talking about that inkjet printer attached via USB there probably isn’t much to worry about. But steps should be taken with any wireless or ethernet printer.
Steps to Secure a Printer
Any printer can be secured by these measures:
- Not entering in a gateway address
- Changing the default password
- Turning off unnecessary protocols
- Keeping the firmware up to date.
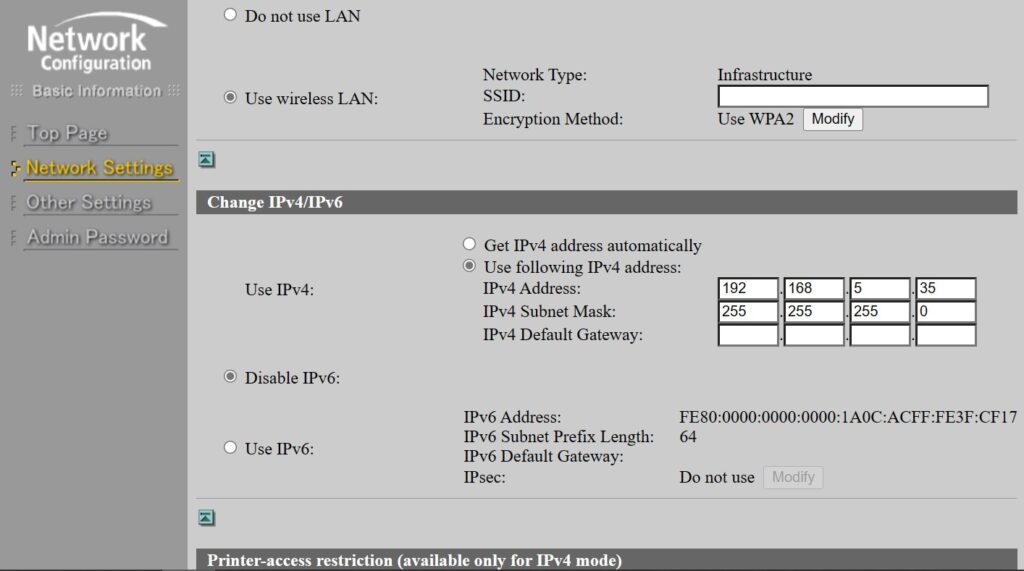
While WPS makes wireless setup easy, the DHCP server provides the printer with a gateway IP. Which also gives it access to the internet.
It’s fine to initially setup a printer this way. But in my experience changing a printer from DHCP to a static IP with a blank gateway is the best way to secure a printer. This means it can only print or scan to the local network. Cloud services or contacting the manufacturer won’t work.
Change the Default Password
Changing the password protects the firmware and file system from unauthorized changes. Almost every inkjet and laser printer has an embedded web interface, which is hosted on the LAN. Default passwords are public knowledge and cat be exploited easily.
Changing the default password blocks easy access to your printer from any device on your network. Any information stored for scan to email or scan to file is also protected.
Disable Unnecessary Protocols
Extra protocols allow for easy setup and status messages. If you don’t mind sacrificing those then you’ll gain a more secure device.
Printing or scanning still work with other protocols disabled. Which is all it should be doing on your network anyway.
Disabling these protocols lightens the traffic on your LAN and makes it more secure. Unnecessary protocols are:
- UPNP
- Bonjour
- SNMP
- SMB
- IP6
UPNP poses the highest risk. While it enables smart devices such as Refrigerators, Coffee makers, and TV’s to connect to the internet. It’s also the most vulnerable to attacks. You should turn this protocol off at your router as well.
Bonjour makes setting up printers easy but it’s also vulnerable to attacks. In my experience, printers setup with Bonjour don’t print as fast as other ports. They also have connection issues down the road.
SNMP is nice if you have to manage a fleet of printers. It’s totally unnecessary for handling several printers at home or a small business. In my experience SNMP is frequently responsible for erroneous offline printers.
Printers don’t need IP6 to communicate. Especially on a LAN. I recommend disabling IP6 on any printer.
Keep Firmware Up to Date
Firmware updates are a two edged sword. On the one hand, they keep the printer secure and fix problems. On the other hand, they cause problems with toner and ink cartridges. Firmware updates commonly cause printers to reject any non-OEM cartridges installed.
A ink tank printer avoids those issues. Some laser printers can be reset after a firmware update.
From what I’ve seen firmware updates do contain a lot of security updates and fixes. I usually wait until an update is at least a week old before installing it. If the firmware update causes any problems it will be apparent by then.
Final Thoughts
Lexmark and HP printers are leading the industry with built in security for unauthorized access or firmware changes. But it wasn’t too many years ago printer security was lacking.
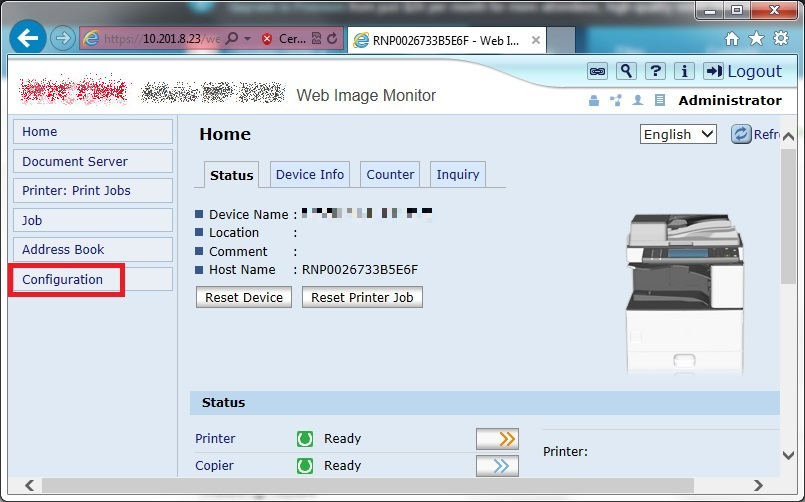
Certain manufacturers unintentionally hosted their printers web interface on the internet. What should have been only visible on a LAN wound up being visible on the internet.
A search for web image monitor, for instance, would return results for any MFP’s that had gateway and DNS address entered. Basically, anybody on the internet could access the web interface of these MFP’s.
User names and passwords for scan to file or email shortcuts were stored in an XML format. Any unfortunate company that hadn’t changed the default password put this data at risk.
While there’s no longer a risk like that, many all in ones can communicate over the internet. While there is little risk with these communications, there are a few things to keep in mind when hooking up devices to your network.
FAQ
Home printers need secured just as any business printer would.
Printers are secured by these steps
1. Turn off unnecessary protocols, such as Bonjour, UPNP, or SNMP.
2. Change default passwords.
3. Keep firmware up to date.
Sharing a printer enables protocols, discovery tools, and access to file systems on the network. Printers are as vulnerable as any other computer on the network.
Wireless printers need secured as any wireless device.

The Copier Guy, aka Dave. I’ve worked on scanners, printers, copiers, and faxes over 23 years. When I’m not fixing them I’m writing about them. Although, I’m probably better at fixing them. I have certificates from Canon, Xerox. Ricoh, Kyocera, Lexmark, HP, and Konica Minolta. My experience includes other brands as well as several types of processes. If it uses paper I’ve probably worked on one.





Leave a Reply